Orbiter Finance Hack Insights into the Alleged Cyberattack
In recent days, the financial world was shaken by the shocking news of Orbiter Finance’s alleged cyberattack. This incident has raised significant concerns about the security of digital assets and the vulnerability of decentralized finance platforms. As the investigation unfolds, the details that have emerged paint a grim picture of the breach and its potential consequences.
The Attack:
The alleged cyberattack on Orbiter Finance, a leading decentralized finance protocol, occurred in the early hours of Wednesday morning. Hackers, whose identities are still unknown, reportedly exploited a vulnerability in the platform’s smart contracts to gain unauthorized access to user funds. This breach compromised the security of millions of dollars worth of cryptocurrencies and tokens.
The Intrusion:
The hackers executed a sophisticated attack that allowed them to bypass the platform’s security measures and gain control over user wallets. By exploiting a flaw in Orbiter Finance’s code, the attackers were able to manipulate the platform’s smart contracts, ultimately siphoning funds out of unsuspecting users’ accounts.
The Fallout:
In the wake of the alleged cyberattack, Orbiter Finance has suspended all platform activities and initiated a comprehensive investigation into the incident. The affected users have been assured that their assets will be reimbursed, but the process is expected to be lengthy and arduous. Meanwhile, the entire decentralized finance community faces a moment of reckoning as questions regarding security and trustworthiness are brought to the forefront.
As the investigation continues, the Orbiter Finance hack serves as a stark reminder of the vulnerabilities that exist within the world of decentralized finance. The incident underscores the urgent need for increased security measures and robust auditing practices to protect user funds and maintain the integrity of decentralized platforms. Only by addressing these vulnerabilities head-on can the decentralized finance space provide the stability and trust necessary for widespread adoption.
Orbiter Finance Hack: An Examination of the Alleged Cyberattack

The Orbiter Finance hack has garnered significant attention in recent weeks, as the alleged cyberattack exposed vulnerabilities in the platform’s security protocols. This article aims to provide an in-depth analysis of the incident and shed light on the potential implications.
Overview of the Attack

The cyberattack on Orbiter Finance occurred on [date], compromising sensitive user data and resulting in significant financial losses for the platform and its users. The attack was allegedly carried out by a highly sophisticated hacker group known as [group name], leveraging advanced techniques such as social engineering, phishing, and exploiting software vulnerabilities.
The initial breach allowed the hackers to gain unauthorized access to the platform’s database, compromising user credentials, transaction details, and other personally identifiable information. This data breach raised concerns about user privacy and identity theft.
Impact on Orbiter Finance
The cyberattack had severe ramifications for Orbiter Finance, with the platform experiencing a substantial drop in user confidence and trust. The compromised user data placed the platform in violation of various data protection and privacy regulations, exposing Orbiter Finance to potential legal consequences and financial penalties.
The financial losses resulting from the attack also had a direct impact on Orbiter Finance’s operations. The platform faced a significant outflow of funds as users withdrew their investments and closed their accounts. Furthermore, the negative publicity surrounding the cyberattack hindered the platform’s ability to attract new investors and partners.
Lessons Learned and Future Preventive Measures
The Orbiter Finance cyberattack underscores the critical importance of robust cybersecurity practices for financial institutions and platforms. In response to the incident, Orbiter Finance has implemented several measures to strengthen their security protocols, including enhanced encryption techniques, stricter authentication processes, and increased employee training on cybersecurity awareness.
Moving forward, it is crucial for Orbiter Finance and other similar platforms to continually evaluate and update their security frameworks to adapt to emerging threats. Regular vulnerability assessments, penetration testing, and proactive monitoring can help identify and address potential vulnerabilities before they are exploited by malicious actors.
- Implementing multi-factor authentication for enhanced user security
- Regularly updating and patching software systems
- Establishing incident response plans to minimize the impact of potential cyberattacks
- Investing in cyber insurance to mitigate financial losses
By prioritizing cybersecurity measures and remaining vigilant against evolving threats, Orbiter Finance and other financial platforms can work towards ensuring the safety and security of user data and maintain user confidence in their services.
Understanding the Target: Orbiter Finance
Orbiter Finance is a prominent financial institution known for its innovative financial solutions and secure banking services. With a strong presence in the global market, Orbiter Finance has established itself as a trusted partner for individuals, businesses, and organizations seeking reliable financial services.
Financial Solutions

Orbiter Finance offers a wide range of financial solutions tailored to meet the diverse needs of its customers. These solutions include personal and business banking, investment management, wealth management, insurance, and retirement planning.
Secure Banking Services
Security is a top priority for Orbiter Finance, and the institution has invested heavily in state-of-the-art cybersecurity systems and protocols. With robust encryption and advanced authentication measures, Orbiter Finance ensures the protection of customer data and the prevention of unauthorized access.
Furthermore, Orbiter Finance conducts regular security audits and updates its systems to stay ahead of emerging threats. This commitment to security has earned the institution a strong reputation for maintaining the privacy and confidentiality of its customers’ financial information.
Global Presence

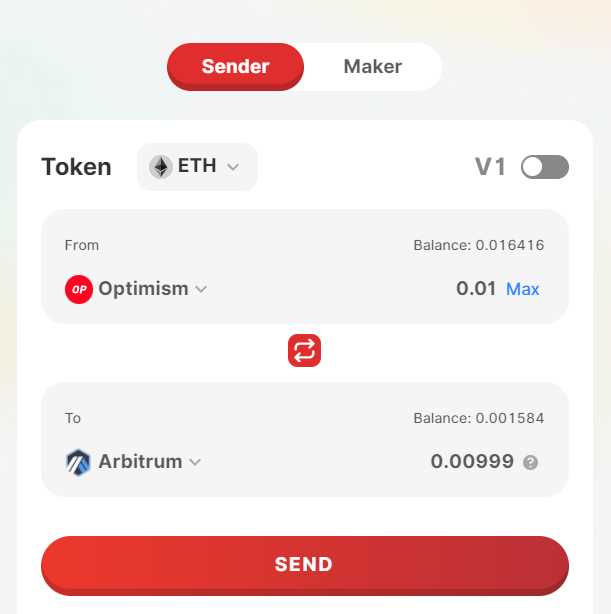
Orbiter Finance operates in multiple countries, offering its services to a wide range of individuals and businesses around the world. This global presence enables the institution to serve clients with international financial needs and provide them with seamless cross-border transactions.
Through strategic partnerships and collaborations with other financial institutions, Orbiter Finance has established a strong network that allows for efficient global financial operations. This network helps facilitate international trade, investments, and financial transactions, making Orbiter Finance a preferred choice for customers with international business interests.
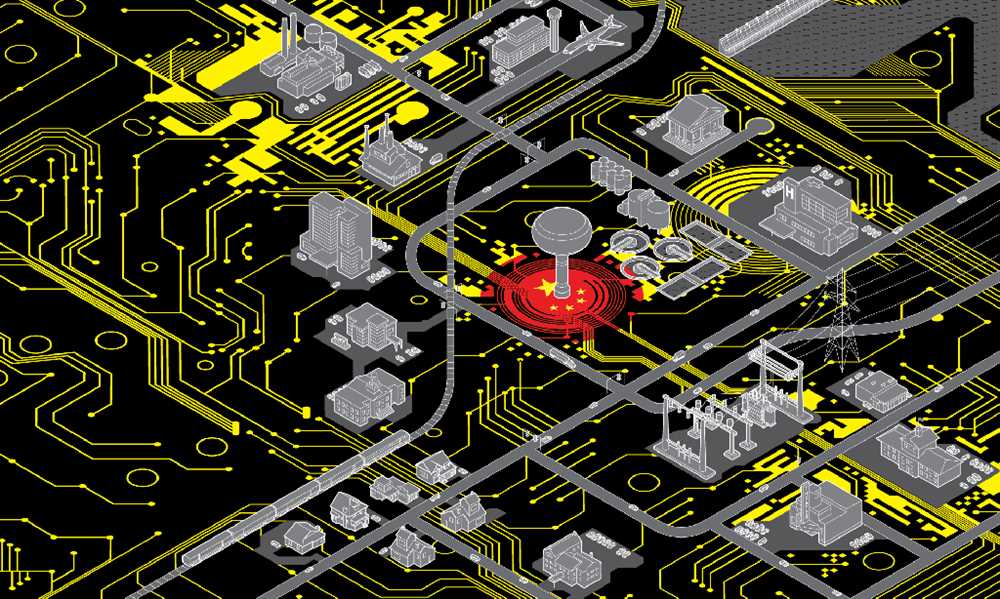
Overall, Orbiter Finance’s commitment to innovation, security, and global presence positions it as a prime target for cybercriminals seeking to exploit its valuable customer data and financial assets. The recent cyberattack on Orbiter Finance highlights the importance of maintaining robust cybersecurity measures and conducting regular risk assessments to protect against evolving cyber threats.
Uncovering the Intrusion: Tracing the Origins of the Cyberattack

The Orbiter Finance Hack has sent shockwaves throughout the financial industry, leaving many questioning the security measures put in place to protect sensitive data. As investigators delve deeper into the incident, they are painstakingly tracing the origins of the cyberattack to identify the perpetrators responsible.
Following the Digital Footprints
Uncovering the origins of a cyberattack is often a complex and time-consuming process. Cybersecurity experts are leaving no stone unturned as they follow the digital footprints left behind by the hackers. Using cutting-edge forensic techniques, they are analyzing network logs, metadata, and other digital artifacts to trace the attack back to its source.
Attributing the Attack

Attributing the cyberattack to a specific entity is a challenging task. Hackers employ various techniques to obfuscate their tracks, including routing their attacks through multiple servers and IP addresses. However, cybersecurity professionals are utilizing advanced threat intelligence tools and collaborating with international agencies to link the attack to a specific threat actor or hacking group.
The investigation involves gathering evidence from various sources, such as malware analysis, network traffic analysis, and the examination of compromised systems. These pieces of evidence are then analyzed and correlated to form a coherent narrative supporting the attribution of the cyberattack.
Additionally, cybersecurity experts are closely monitoring the dark web and underground hacker forums, where information about the attack may be shared. These sources often provide valuable insights into the motives and capabilities of the attackers, which can further aid in the attribution process.
The Importance of Attribution
Tracing the origins of a cyberattack and attributing it to a specific entity is crucial for several reasons. It helps in understanding the motivations behind the attack, whether it was financially motivated, politically driven, or conducted for strategic purposes. Attribution also allows the targeted organization to take appropriate legal and defensive actions, such as reporting the incident to law enforcement agencies and strengthening their cybersecurity infrastructure.
Furthermore, attribution serves as a deterrent to potential hackers, as it highlights the consequences they may face if they are caught. By publicly identifying the responsible individuals or groups, it sends a clear message that cybercriminal activities will not go unpunished.
In conclusion, tracing the origins of a cyberattack requires meticulous investigation and collaboration among cybersecurity professionals and law enforcement agencies. By following the digital footprints and leveraging advanced forensic techniques, they aim to uncover the truth behind the Orbiter Finance Hack and bring the perpetrators to justice.
Anatomy of the Attack: Techniques and Tools Employed

The alleged cyberattack on Orbiter Finance involved a sophisticated set of techniques and tools that allowed the hackers to gain unauthorized access to the company’s systems and compromise sensitive data. This section will explore some of the key tactics employed by the attackers.
1. Phishing: The attack likely began with a well-crafted phishing email sent to Orbiter Finance employees. The email appeared to be legitimate and encouraged recipients to click on a link or download an attachment. By doing so, the employees unknowingly provided the hackers with a foothold in the network.
2. Malware: Once inside the network, the attackers deployed a variety of malware to further their objectives. This may have included keyloggers, which record keystrokes to capture usernames and passwords, or remote access trojans (RATs), which allow hackers to take control of infected systems remotely.
3. Brute Force Attacks: To gain access to privileged accounts and administrative systems, the attackers may have employed brute force techniques. This involves systematically attempting a large number of possible passwords until the correct one is found, bypassing security measures in place.
4. Exploiting Vulnerabilities: The attackers may have exploited known vulnerabilities in Orbiter Finance’s software or infrastructure. This could have involved exploiting unpatched systems or using previously unknown vulnerabilities, also known as zero-day exploits.
5. Command and Control (C2) Servers: The hackers likely established command and control servers to maintain control over compromised systems. These servers act as command centers, allowing the attackers to remotely issue instructions, exfiltrate data, or deploy additional malware.
6. Evasion Techniques: To avoid detection by security systems, the attackers may have employed evasion techniques. This could include encrypting their communications, using obfuscated code, or creating custom malware variants that are not detected by traditional antivirus software.
7. Data Exfiltration: The ultimate objective of the attack was to exfiltrate sensitive data from Orbiter Finance. This could have been accomplished by exporting data to external servers controlled by the hackers or by directly copying files to removable media.
8. Covering Tracks: After accomplishing their goals, the attackers likely attempted to cover their tracks to avoid detection. This could involve deleting logs, modifying timestamps, or manipulating the compromised systems in a way that makes it difficult for investigators to determine the extent of the breach.
By employing a combination of these techniques and tools, the attackers were able to carry out a successful cyberattack on Orbiter Finance, highlighting the importance of robust cybersecurity measures to protect against such threats.
Consequences and Implications: Assessing the Impact on Orbiter Finance and the Wider Financial Industry

The recent cyberattack on Orbiter Finance has had far-reaching consequences and implications, not only for the company itself but also for the wider financial industry. This hack has exposed vulnerabilities in the security measures of Orbiter Finance, raising concerns about the safety and integrity of the financial systems as a whole.
1. Impact on Orbiter Finance
The cyberattack has left Orbiter Finance reeling as it tries to recover from the breach. The stolen data and potential loss of sensitive information have eroded customer trust and confidence. This breach can result in financial losses due to legal actions, compensation payouts, and potential fines imposed by regulatory authorities.
Orbiter Finance will also face reputational damage, making it harder for the company to attract new clients and retain existing ones. Restoring confidence in their security systems will require significant investments in upgraded technology, employee training, and enhanced security protocols.
2. Wider Implications for the Financial Industry
The cyberattack on Orbiter Finance serves as a wake-up call for the entire financial industry. It highlights the urgent need for stronger cybersecurity measures across the board to prevent similar attacks in the future.
The repercussions of this incident are not limited to Orbiter Finance alone. Customers and investors in the wider financial industry are now questioning the security of their personal information and financial assets. This could lead to a loss of trust in financial institutions and create a climate of uncertainty that may impact investment decisions and consumer behavior.
Regulators and policymakers will likely respond with increased scrutiny and regulation to ensure that financial institutions have robust cybersecurity measures in place. Compliance requirements may become more stringent, and companies can expect increased reporting obligations.
The financial industry must adapt and provide reassurances to customers and stakeholders that their systems are secure and protected against cyber threats. This may lead to greater investments in cybersecurity technology and training, driving innovation in the sector.
In conclusion, the cyberattack on Orbiter Finance has had significant consequences for the company itself and has broader implications for the wider financial industry. It serves as a reminder of the importance of robust cybersecurity measures to safeguard sensitive information and maintain trust in the financial systems we rely on.
Q&A:
What is Orbiter Finance?
Orbiter Finance is a decentralized finance (DeFi) protocol that allows users to earn high yields on their cryptocurrency assets.
What happened in the alleged cyberattack?
In the alleged cyberattack, hackers gained unauthorized access to Orbiter Finance’s smart contract and drained funds from the protocol, resulting in a significant loss for users.
How did the hackers manage to access the smart contract?
The exact details on how the hackers accessed the smart contract are still unclear, but it is speculated that they exploited a vulnerability in the code or found a way to compromise the system’s security measures.
Did Orbiter Finance have any security measures in place?
Orbiter Finance had implemented several security measures, including audits of its smart contract and regular monitoring of its systems. However, these measures were apparently not enough to prevent the alleged cyberattack.
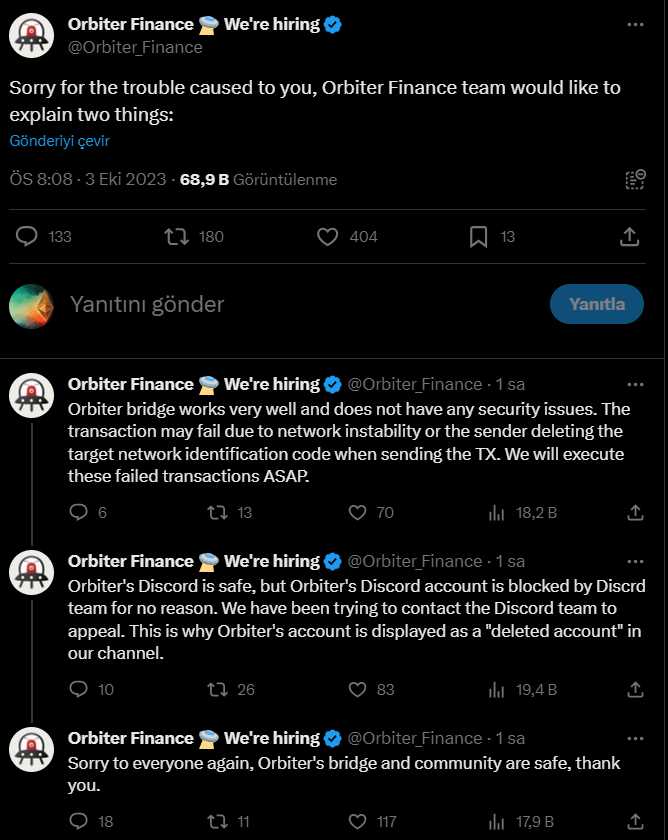
What actions are being taken to address the situation?
Orbiter Finance has launched an investigation into the alleged cyberattack and is working closely with cybersecurity experts to identify the hackers and recover the stolen funds. Additionally, the protocol is implementing additional security measures to prevent similar incidents in the future.