Lessons Learned Strengthening Orbiter Finances Security Post Attack

In today’s digital age, financial institutions are facing unprecedented threats from cybercriminals. With the increasing adoption of online banking and digital payment systems, it has become imperative for these institutions to ensure the security and integrity of their customers’ financial information. The recent attack on Orbiter Finance has served as a wake-up call for the entire industry, highlighting the vulnerabilities and weaknesses that exist in the current security measures.
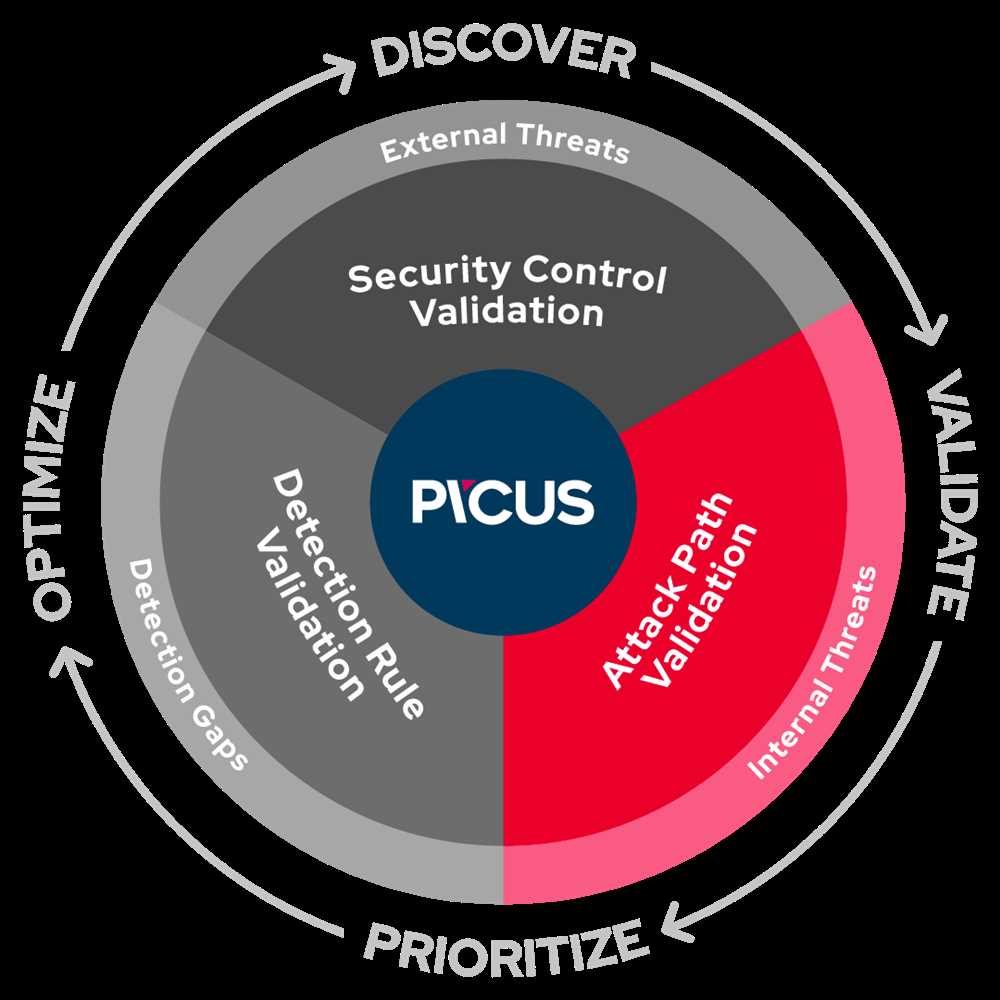
One of the key lessons learned from the attack on Orbiter Finance is the importance of implementing a multi-layered security approach. A single layer of security is no longer sufficient to deter highly skilled cybercriminals. Institutions must invest in robust security protocols that include not only firewalls and antivirus software, but also advanced threat detection systems, encryption technologies, and user authentication mechanisms.
Furthermore, the attack on Orbiter Finance has highlighted the crucial role that employee awareness and training play in maintaining and enhancing security. Phishing attacks and social engineering techniques have become increasingly sophisticated, making it imperative for employees to be vigilant and cautious when dealing with suspicious emails or phone calls. Regular training programs should be conducted to educate employees about the latest cybersecurity threats and best practices for mitigating these risks.
Lastly, the incident has underscored the need for financial institutions to collaborate and share information with each other and relevant authorities. Cybercriminals often target multiple institutions, and by sharing information about potential threats and vulnerabilities, institutions can collectively strengthen their defenses. This collaboration should also extend to third-party vendors and service providers who have access to sensitive financial data.
While the attack on Orbiter Finance was undoubtedly a setback, it serves as a valuable opportunity for the entire industry to learn, adapt, and strengthen its security measures. By implementing a multi-layered security approach, investing in employee training, and fostering collaboration, financial institutions can better protect themselves and their customers from cyber threats in the future.
In conclusion, the attack on Orbiter Finance has highlighted the urgent need for financial institutions to enhance their security measures. By implementing a multi-layered security approach, investing in employee training, and fostering collaboration, institutions can mitigate the risks posed by cybercriminals and protect their customers’ financial information.
Understanding the Attack
When it comes to strengthening finance security, understanding the nature of the attack is crucial. By learning from past incidents and analyzing the attack, organizations can better prepare themselves for future threats. In the case of Strengthening Orbiter Finance Security, there are several key lessons that have been learned from the post-attack analysis.
Identification and Analysis
In order to effectively respond to an attack, it is essential to properly identify and analyze the nature of the attack. This includes understanding the attack vector, the vulnerabilities exploited, and the tactics employed by the attackers.
During the investigation of the Orbiter Finance attack, it was discovered that the attackers gained access through a phishing email that targeted an employee with administrative privileges. This highlights the importance of employee awareness training and the need for robust email security measures.
Timely Response and Containment

The speed at which an organization responds to an attack can greatly impact the extent of the damage. In the case of the Orbiter Finance attack, a timely response allowed the security team to quickly contain the breach and prevent further compromise.
By isolating affected systems, suspending compromised accounts, and conducting a comprehensive analysis of the attack, Orbiter Finance was able to limit the impact and prevent significant financial losses.
The key lesson learned here is the importance of proactive monitoring and rapid incident response capabilities.
Effective incident response involves having well-defined protocols and processes in place, as well as a skilled team that is trained to handle such situations efficiently.
Enhancing Security Measures
Understanding the attack can also provide valuable insights into weaknesses in existing security measures. By analyzing the attack, organizations can identify areas where their defenses were insufficient and take appropriate actions to strengthen those areas.
For example, in the case of the Orbiter Finance attack, it was identified that the lack of multi-factor authentication for privileged accounts was a major vulnerability. As a result, Orbiter Finance implemented stronger authentication mechanisms to prevent unauthorized access.
It is crucial for organizations to continuously evaluate and enhance their security measures to stay ahead of evolving threats.
By understanding the attack and applying the lessons learned, organizations like Orbiter Finance can effectively strengthen their finance security and better protect against future attacks.
How the Orbiter Finance System was Compromised
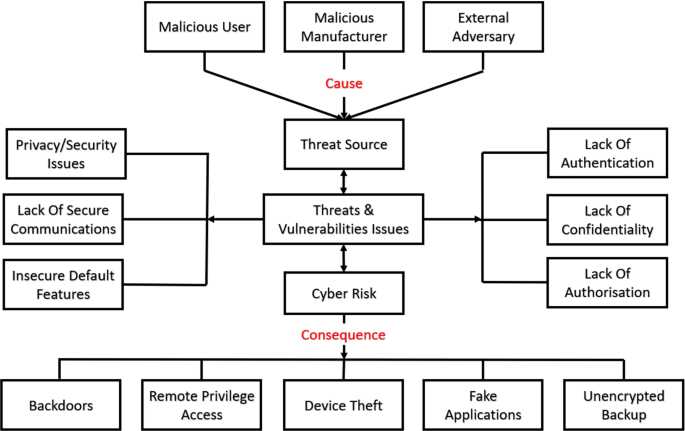
The compromise of the Orbiter Finance System was a result of various vulnerabilities that were exploited by attackers. This section provides an overview of the key factors that led to the compromise.
1. Inadequate Security Measures
One of the main reasons behind the compromise was the inadequate security measures in place within the Orbiter Finance System. This included weak authentication mechanisms, lack of encryption protocols, and insufficient network security configurations. These vulnerabilities provided an easy entry point for attackers to gain unauthorized access to the system.
2. Phishing Attacks
Phishing attacks played a significant role in the compromise of the Orbiter Finance System. Attackers used deceptive emails, text messages, or phone calls to trick employees into disclosing sensitive information such as their login credentials. Once the attackers obtained these credentials, they were able to gain unauthorized access to the system and carry out malicious activities.
3. Software Vulnerabilities
Software vulnerabilities were also exploited by attackers to compromise the Orbiter Finance System. These vulnerabilities could exist in various components of the system, including the operating system, web applications, or third-party software. Attackers would search for and exploit these vulnerabilities to gain unauthorized access or perform unauthorized actions within the system.
4. Insider Threats
Insider threats, either intentional or unintentional, played a role in the compromise of the Orbiter Finance System. This could include employees with malicious intent or employees who unknowingly engaged in risky behavior, such as clicking on phishing links or sharing sensitive information with unauthorized individuals. These actions provided opportunities for attackers to exploit the system’s vulnerabilities.
5. Weak Password Practices

Weak password practices within the Orbiter Finance System also contributed to the compromise. This included the use of easily guessable passwords, reuse of passwords across multiple accounts, and lack of password expiration policies. Attackers could use various methods, such as brute force attacks or password spraying, to gain unauthorized access to accounts and the overall system.
Addressing these vulnerabilities and implementing stronger security measures is crucial for preventing future compromises of the Orbiter Finance System and ensuring the protection of sensitive financial data.
Recovering from the Attack
Recovering from a cybersecurity attack requires a swift and effective response to minimize damage and restore normal operations. Here are some key steps to consider when recovering from an attack:
- Containment: The first step is to isolate the affected systems to prevent further spread of the attack. This may involve disconnecting infected machines from the network or segmenting the network to contain the breach.
- Assessment: Once the attack has been contained, it is important to assess the extent of the damage and gather information about the attack. This involves identifying the type of attack, the systems and data compromised, and any vulnerabilities that were exploited.
- Remediation: After assessing the damage, remediation efforts can begin. This may involve patching vulnerabilities, removing malware, and restoring affected systems from backups. It is important to follow best practices and work with cybersecurity professionals to ensure a thorough and effective remediation process.
- Enhancing security: Recovering from an attack is an opportunity to enhance the overall security posture. This includes implementing stronger security controls, conducting regular security audits, and providing cybersecurity training to staff to prevent future attacks.
- Communication: Open and transparent communication is crucial during the recovery process. Stakeholders, including customers, partners, and employees, should be informed about the attack, the steps taken to recover, and any potential impacts on their data or operations. This helps to maintain trust and manage expectations.
- Monitoring and response: Even after the initial recovery, it is important to continue monitoring systems and networks for any signs of further compromise. Incident response plans should be in place to respond quickly to any potential threats or breaches.
By following these steps and learning from the attack, organizations can strengthen their resilience to future cyber threats and protect the financial security of their orbiters.
Steps Taken to Restore the Finance System

After the security attack on the Orbiter Finance system, several immediate steps were taken to restore the stability and security of the financial operations. These steps included:
1. Isolating and Analyzing the Attack
The first step taken was to isolate and analyze the attack. This involved identifying the entry points, the malicious code used, and the extent of the damage caused. This allowed the team to understand the vulnerabilities in the system and develop a strategy for remediation.
2. Implementing Enhanced Security Measures
To prevent future attacks, enhanced security measures were implemented across the finance system. This included updating firewalls and intrusion detection systems, strengthening access controls, and implementing multi-factor authentication for all users. Regular security audits and penetration testing were also scheduled to identify and address any potential vulnerabilities.
3. Restoring Data and System Integrity
The next step was to restore the integrity of the data and the finance system. This involved rebuilding the affected portions of the system, restoring backups of data, and ensuring data consistency and accuracy. The team worked diligently to ensure that the system was fully functional and that all financial data was secure and accessible.
4. Educating and Training Employees
As part of the recovery process, employees were provided with training and education on cybersecurity best practices. This included awareness programs on phishing attacks, social engineering, and the importance of strong passwords. By educating employees, the organization aimed to create a culture of security awareness and prevent future security incidents.
5. Monitoring and Incident Response
A robust monitoring and incident response system was implemented to detect and respond to any suspicious activities. Real-time monitoring allowed for immediate action to be taken if any unauthorized access or suspicious behavior was detected. Incident response plans were also developed to ensure a prompt and effective response in the event of a security incident.
A comprehensive and systematic approach was taken to restore the finance system after the attack. By implementing enhanced security measures, restoring data integrity, educating employees, and implementing a strong incident response system, Orbiter Finance was able to restore the security of its finance operations and prevent future attacks.
Key Lessons Learned
After a recent security attack on Orbiter’s finance system, several key lessons were learned. These lessons provide valuable insights for strengthening the security of the system and preventing future attacks.
Lesson 1: Implement a Multi-Layered Security Approach
One of the main lessons learned from the attack is the importance of implementing a multi-layered security approach. This means employing multiple security measures at different levels, including network security, application security, and user access controls. By having multiple layers of security in place, the chances of a successful attack are significantly reduced.
Lesson 2: Regularly Update and Patch Software

Another key lesson is the importance of regularly updating and patching software. Outdated software often contains vulnerabilities that can be exploited by attackers. By staying up to date with software updates and patches, Orbiter can ensure that any known vulnerabilities are mitigated, reducing the potential attack surface.
Lesson 3: Conduct Regular Security Audits
It is crucial for Orbiter to conduct regular security audits to identify and address any potential security weaknesses. These audits should include thorough testing of the system for vulnerabilities, penetration testing, and code reviews. By proactively identifying and addressing any weaknesses, Orbiter can improve the overall security posture of its finance system.
Lesson 4: Educate Users on Security Best Practices
Users play a critical role in maintaining the security of the finance system. It is important to educate users on security best practices, such as strong password management, avoiding suspicious links and attachments, and being cautious when sharing sensitive information. By promoting a strong security culture among users, Orbiter can reduce the likelihood of successful attacks.
Lesson 5: Establish Incident Response and Recovery Plans
In the event of a security breach, it is essential for Orbiter to have well-defined incident response and recovery plans in place. These plans should outline the steps to be taken immediately following an attack, including isolating affected systems, notifying relevant stakeholders, and initiating recovery processes. By having a solid plan in place, Orbiter can minimize the impact of an attack and ensure a swift recovery.
By applying these key lessons learned from the recent security attack, Orbiter can significantly strengthen the finance system’s security and better protect against future threats.
Identifying Vulnerabilities and Weaknesses
In order to strengthen Orbiter Finance’s security, it is crucial to identify and address potential vulnerabilities and weaknesses that can make the system prone to attacks. This section highlights some key steps that can be taken to identify and mitigate such risks:
1. Regular Vulnerability Assessments
Conducting regular vulnerability assessments is essential to identify any weaknesses in the system’s infrastructure, networks, and applications. These assessments should be performed by knowledgeable and experienced professionals who can analyze the system thoroughly and identify any potential vulnerabilities that could be exploited by attackers.
2. Penetration Testing
Penetration testing involves launching controlled attacks on a system to identify its vulnerabilities. This can help simulate real-world attack scenarios and provide valuable insights into the system’s weaknesses. It is important to engage skilled ethical hackers who are adept at identifying and exploiting vulnerabilities without causing any harm to the system.
3. Implementing Security Measures
Based on the findings of vulnerability assessments and penetration testing, it is crucial to implement appropriate security measures to mitigate the identified risks. This may involve implementing firewalls, intrusion detection systems, secure protocols, access controls, and encryption mechanisms to protect sensitive data and prevent unauthorized access.
Moreover, it is important to stay up-to-date with the latest security patches and updates for all software and hardware components of the system. Regularly patching and updating systems can help fix known vulnerabilities and prevent attackers from exploiting them.
4. Continuous Monitoring
Continuous monitoring of the system is essential to identify any suspicious activities or anomalies that may indicate a potential attack or security breach. Implementing robust monitoring tools and techniques, such as log analysis and intrusion detection systems, can help detect and respond to security incidents in a timely manner.
5. Employee Training and Awareness
Human error is often a major factor in security breaches. Providing comprehensive training to employees on security best practices, such as strong password policies, phishing awareness, and safe browsing habits, can significantly reduce the risk of attacks. Regular security awareness campaigns and workshops can help employees stay vigilant and make informed decisions to protect the system and its data.
In conclusion, identifying vulnerabilities and weaknesses in Orbiter Finance’s systems is crucial for strengthening its overall security. By conducting regular vulnerability assessments, penetration testing, implementing security measures, continuously monitoring the system, and providing employee training and awareness, Orbiter Finance can effectively mitigate risks and safeguard its financial operations.
FAQ:
Why is strengthening orbiter finance security important?
Strengthening orbiter finance security is important because cyber attacks on financial institutions can have severe consequences, including theft of funds, disruption of services, and damage to a company’s reputation. By implementing robust security measures, financial institutions can better protect themselves and their customers from these threats.
What are some key lessons learned post-attack?
Some key lessons learned post-attack include the importance of regularly updating security systems and software, training staff on cybersecurity best practices, and conducting thorough audits to identify and address vulnerabilities. Additionally, it is crucial for financial institutions to have incident response plans in place to quickly and effectively respond to attacks.